Menu


Getting Started Fishing
Amanda Olsen
April 19, 2024

Double Emergence: Cicadas Taking Over Midwest
Amanda Olsen
April 12, 2024

Sloth Saga Enters New Phase
Cole McDonnell
April 5, 2024

Opponents Of ‘Blakeman’s Militia’ Rally In Mineola
Janet Burns
April 12, 2024
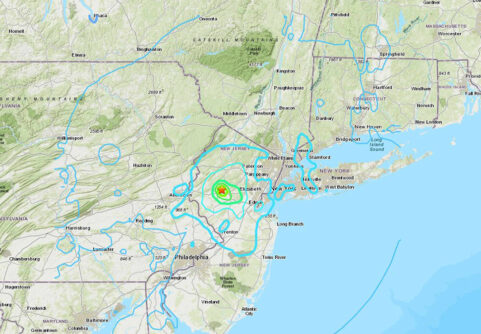
Rare Earthquake Shakes The Region
Anton Media Group Staff
April 5, 2024
Total Eclipse 2024
Amanda Olsen
April 5, 2024
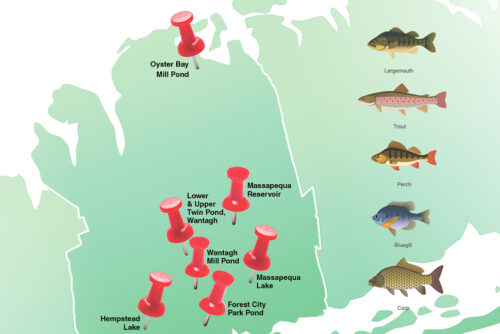
Freshwater Fishing In Nassau
Amanda Olsen
April 1, 2024

Can The MTA Manage $15 Billion Carryover Capital Projects With The Next $51 Billion Or More
Larry Penner
April 15, 2024

Shine A Light For Charity On The INN
Kayla Donnenfeld
April 15, 2024

The Big Move
Marisa Cohen
April 15, 2024

We Would Not Miss MS
Patty Servidio
April 8, 2024
LOCAL EDITIONS
TRENDING
Ukrainian Rocker Talks
Fundraising For Friends,
25 Years Of Touring
Gogol Bordello to play free benefit
in Tompkins Square Park
By Cory Olsen – April 15, 2024
THIS WEEK'S
SPECIAL SECTIONS